- Saviynt Forums
- Enterprise Identity Cloud Discussions
- Identity Governance & Administration
- Update an account attribute on an endpoint based o...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/06/2024 11:42 AM
My use case is to update isCallcenter attribute on a target EP1 (SaaS application) based on an AD group provisioned in target EP2 (Active Directory).
Users will request an AD entitlement on EP2 which when provisioned must trigger an update automatically to EP1 to update the isCallcenter attribute.
How can this be done through a seamless unified process within Saviynt without having to schedule an actionable analytics at a regular frequency? Having an actionable analytics is a disjoint solution.....
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/06/2024 12:15 PM
Hi @krecpond ,
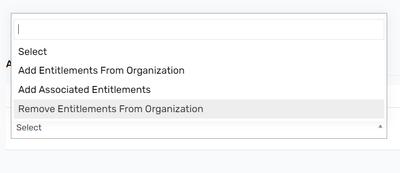
One solution could be that you create an entitlement type in ep 1 and a dummy entitlement. Map it with AD entitlement using entitlement map or associated entitlement.
When Somebody request ad entitlement, a task for this other endpoint dummy ent will also be created.
In your provisioning json, you can make update account API call for that ent type add access.
Hope it works!! And also suits your needs.
You can also wait for more ideas but let me know if this works for you.
Br,
Amit
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/06/2024 12:25 PM
This will not work because we already have add access json configured for EP1. We cannot replace that with an update account JSON.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/06/2024 01:04 PM - edited 02/06/2024 01:18 PM
Hi @krecpond , that is why we are creating a new entitlement type else would have created the dummy entitlement in existing one, right.
You can have separate calls for different ent types. Like in Azure ad , aadgroup has its json, directory role has its own.
Similar way with this new entitlement type, use update account APIs. Like below :
{
"call": [
{
"name": "SKU",
"connection": "userAuth",
"url": "https://graph.microsoft.com/v1.0/users/${account.accountID}/assignLicense",
"httpMethod": "POST",
"httpParams": "{\"addLicenses\": [{\"disabledPlans\": [],\"skuId\": \"${entitlementValue.entitlementID}\"}],\"removeLicenses\": []}",
"httpHeaders": {
"Authorization": "${access_token}"
},
"httpContentType": "application/json",
"successResponses": {
"statusCode": [
200,
201,
204,
205
]
}
},
{
"name": "DirectoryRole",
"connection": "userAuth",
"url": "https://graph.microsoft.com/v1.0/directoryRoles/${entitlementValue.entitlementID}/members/\\$ref",
"httpMethod": "POST",
"httpParams": "{\"@odata.id\":\"https://graph.microsoft.com/v1.0/directoryObjects/${account.accountID}\"}",
"httpHeaders": {
"Authorization": "${access_token}"
},
"httpContentType": "application/json",
"successResponses": {
"statusCode": [
200,
201,
204,
205
]
},
"unsuccessResponses": {
"odata~dot#error.code": [
"Request_BadRequest",
"Authentication_MissingOrMalformed",
"Request_ResourceNotFound",
"Authorization_RequestDenied",
"Authentication_Unauthorized"
]
}
} ] }
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/15/2024 07:48 PM
Thanks @AmitM This approach worked.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/06/2024 03:41 PM
Use request rules
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/06/2024 04:22 PM
Request rules will not work because it has to do with managing entitlements. the requirement is that when user is provisioned to the AD group by Saviynt, Saviynt will automatically populate an attribute on another SaaS target.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
02/06/2024 06:06 PM
You need to go with Actionable analytics only.
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- How to provision entitlements coming from HR source to AD in Identity Governance & Administration
- Assistance on Query || Reportee Access Details in Identity Governance & Administration
- Dynami Attributes action string. in Identity Governance & Administration
- Entitlement owner update in AD in Identity Governance & Administration
- Call datasets information to assign safe to the respective ADgroup in Identity Governance & Administration