- Saviynt Forums
- Enterprise Identity Cloud Discussions
- Identity Governance & Administration
- User update rule "execute on" not working properly
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 12:56 AM
We use user update rules to check if accounts and access needs to be deprovisioned and if the users needs to be disabled.
The user update rule should go as follows: Disable user, disable user accounts (immediately), deprovision access from accounts (immediately) and deprovision account (in 90 days).
When this user update rule triggers for a user, all tasks are created. But when we look at the start date of these tasks, we see that the deprovision access tasks are the same start date as the deprovision account task (90 days). The disable account task start date is correct (the same day).
Can anyone tell us why the deprovision access and deprovision account tasks are the same start date when we explicitly stated that ONLY the deprovision account task should be started in 90 days?
We have also tried adding "0 days" to the deprovision access action, but this did not change anything.
Solved! Go to Solution.
- Labels:
-
Defect or Issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 02:12 AM
Hello @Caesrob,
This is the expected behavior. When we generate future-dated tasks based on rules, the tasks will be initially created on the same day.
However, Saviynt will not process these tasks until the 90-day window has elapsed, even if the provisioning jobs are executed before that time.
Thanks,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 02:32 AM - edited 06/19/2023 02:43 AM
This is exactly the problem we are having though. When I execute these tasks by running a provisioning job, all tasks are executed including the remove account task. There is no 90 day delay on this.
We have also tried re-arranging these tasks so the deprovision account task in 90 days comes first and then the deprovision access task immediately. What this does is set the deprovision of access task on 90 days as well. the disable user account task stays immediate.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 03:23 AM
Hello @Caesrob,
Did you try to put Both rules separately and try?
Thanks,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 04:04 AM
Yes, this works. But we would like it to be 1 rule and not 2 seperate rules. we don't see how this could be an issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 04:06 AM
I have configured the same (both in same rule) in my environment and it works pretty fine. I don't think that would be a issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 04:04 AM
HI @Caesrob,
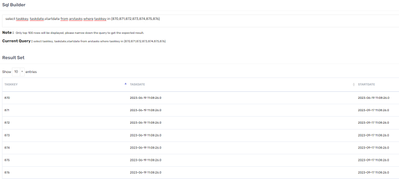
Can you run select taskdate,startdate from arstasks where taskkey in () and share the output for the both disable account and remove access tasks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 04:12 AM
Sure, here is the output. Task 870 is the disable account task, tasks 871-875 are the access removal tasks, task 876 is the account remove task.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 04:16 AM - edited 06/19/2023 04:17 AM
Hi @Caesrob ,
Except task 870 all other tasks will be executed after 90 days. It is fine. What is the issue you are seeing. Tasks get processed based on the startdate.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 04:20 AM
That IS the issue... The remove access tasks should get executed immediately but the remove account task should be executed after 90 days.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/19/2023 04:26 AM
Got it. This is a bug. Rule is taking both account and access as one and creating tasks.
Workaround would be use two different rules
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/20/2023 07:48 AM - edited 06/20/2023 07:49 AM
Hello @Caesrob ,
We are currently conducting internal checks, and for now, you may need to utilize two separate rules for your specific use case.
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/21/2023 06:50 AM
@sudeshjaiswal I have a follow-up question on the Execute On use case. We have configured the rule to disable the account immediately and remove account after 30 days per requirement. However what if the user got rehired within 30 days, does that task need to be discontinued manually?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/21/2023 07:00 AM
Yes, the task would need to be manually discontinued in such a case. Better to have a separate trigger event that calls the rules for remove account as well on the 30th day.
Thanks
Md Armaan Zahir
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/21/2023 07:35 AM
yes thanks! thought so. I believe Actionable Analytics may be a good option to do this.
- UPDATE ACCESS ENDDATE DOESNT WORK in Identity Governance & Administration
- Read User details and ECP value via API not working in Identity Governance & Administration
- AD disablementJSON with logic in Identity Governance & Administration
- Campaign Emails Not being triggered V23.5 in Identity Governance & Administration
- Update Account name into User's CP value using customquery. in Identity Governance & Administration