- Saviynt Forums
- Enterprise Identity Cloud Discussions
- Identity Governance & Administration
- Re: Azure Active Directory multi endpoint request
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Azure Active Directory multi endpoint request
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/30/2022
07:27 AM
- last edited on
06/30/2022
08:19 AM
by
![]() Dave
Dave
- Labels:
-
New Feature Request
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/30/2022 12:39 PM
Hello,
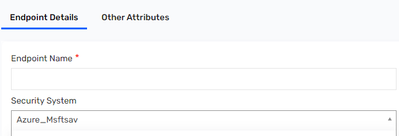
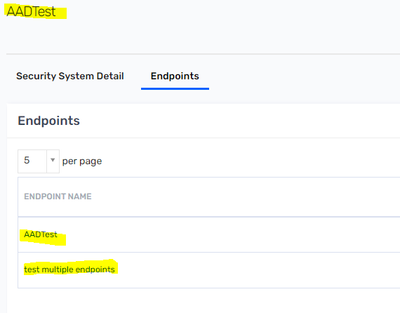
You can achieve this, a security system can be associated with the multiple endpoints, while creating an endpoint you can specify the security system and the endpoint would be associated with it.
Manikanta.S
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/30/2022 01:21 PM
So how should I associate entitlement to the endpoint ? Like Slack entitlement should associate to the Slack endpoint, Github entitlement should associate to the Github endpoint and Altassian entitlement should associate to the Altassian endpoint. All this entitlements are imported from Azure AD. Let me know if you want more clearity on what we are looking for ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
06/30/2022 01:25 PM
Azure AD does not having Group Filter option.
You can do in following way
- Endpoint : Azure - This will pull all information from Azure
- Endpoint Slack - (DB Connector) - Pull information from Saviynt DB (Querying on Azure Endpoint) based on some attributes from Azure endpoint like Customproperty1 = Slack
- Provisioning will happen in Azure but user will see different application
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
07/06/2022 07:24 AM
@rushikeshvartak - Do you have documentation for referring this ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
07/06/2022 07:31 AM - edited 07/06/2022 07:31 AM
Hi @aparikh ,
If you want to create logical apps/endpoints (For different request forms) from entitlements coming from the same Target (here Azure) we would suggest using the REST connector and using the Endpoint Filter Functionality.
The Endpoint filter would create endpoints based off entitlement grouping which can then be used as separate forms for your end users.
Details on the REST connector Documentation : https://saviynt.freshdesk.com/support/solutions/articles/43000521736-rest-connector-guide
Regards,
Sahaj Ranajee
Sr. Product Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
07/12/2022 01:13 PM
Will this work for accounts as well? The request form requires accounts to be of the same endpoint as the entitlement - how would we make Saviynt not generate new accounts for different endpoints within the same security system?
Thanks
Ajit
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
07/15/2022 08:05 AM
The ENDPOINT_FILTER in a REST Connector is only supported for reconciliation and not for provisioning.
The only workaround I can think of is requesting against the parent endpoint, rather than child endpoint.
Avinash Chhetri
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
07/17/2022 11:53 PM
@aparikh As Avinash mentioned, Endpoints_Filter works during recon. For provisioning, since the Connection remains the same. You would need to work your logic of closing the extra new account tasks in the provisioning jsons.
Regards,
Sahaj Ranajee
Sr. Product Specialist
- How to change Request-Option of Entitlement Type in Endpoint Through API in Application Access Governance
- How to Create different tile for All All application with AD in Identity Governance & Administration
- need entitlement import from 2 different OU under logical application in Identity Governance & Administration
- Show entitlements only when boolean (DA) is TRUE in Identity Governance & Administration
- Analytics email to managers about their subordinates in Identity Governance & Administration