- Saviynt Forums
- Enterprise Identity Cloud Discussions
- Identity Governance & Administration
- Re: Filtering Entitlements when importing Accesses...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Filtering Entitlements when importing Accesses and Accounts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/11/2022 04:43 AM
- Labels:
-
Connectors
-
Defect or Issue
-
Imports
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/11/2022 12:02 PM
Are you using endpoint filter option
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/12/2022 02:25 AM
I am not since as far as i understood that only applies for setting up connections with other applications that use Active Directory in this specific case and my goal here is just importing the entitlements (with the filters mentioned) from Active Directory itself.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/12/2022 02:38 AM
Please share connection screenshot
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/12/2022 06:46 AM
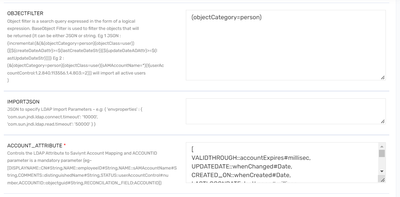
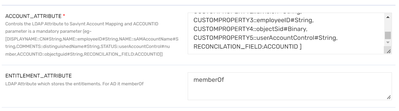
You can find below what i believe should be all the important information in the connection for this topic.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/12/2022 09:17 AM
You can try memberOf Filter
https://confluence.atlassian.com/kb/how-to-write-ldap-search-filters-792496933.html
(&(objectCategory=Person)(sAMAccountName=*)(memberOf=cn=CaptainPlanet,ou=users,dc=company,dc=com))
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/12/2022 09:55 AM
Unfortunately that wouldn't solve my problem. That filter is for persons and my problem is regarding the groups. The filter i currently have for persons is needed when importing accounts, the problem is filtering the groups imported. Our situation is that we want to import accounts and the groups to which those accounts are part of, except some groups that should be filtered according to the restrictions mentioned.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/12/2022 11:27 AM
You can use Endpoint FIlter to achieve your use case
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/13/2022 10:27 AM
Can you please clarify how? I am not understading how can the endpoint filter field help with the entitlement importation?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/13/2022 07:55 PM
Can you refer documentation for same : https://saviynt.freshdesk.com/support/solutions/articles/43000615764-active-directory-ad-connector-g...
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/14/2022 03:09 AM
As referenced in the documentation the endpoints_filter parameter "creates endpoints based on the list of groups specified in the JSON and associates all accounts having access to these groups to the created endpoint." I do not wish to import the groups as endpoints but rather filter the groups that are imported as entitlements when the Import Accounts job is performed with the Entitlement Attribute as memberOf.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/14/2022 04:29 AM
Please confirm if below understanding is correct for your use case
- user1 having group1 to 10
- you want user1 should have only group 1 to group 5 in saviynt
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/18/2022 07:26 AM
Exactly, so after importing both the account and the access only groups 1 to 5 should be on saviynt
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/18/2022 10:30 AM
You can use endpoint filter and create application/endpoint for filtering groups
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/24/2022 09:52 AM
Thanks, i have made some progress. There is still one thing i cant quite resolve. Lets say i want to import all groups except the ones starting with the following,
{"memberOf":["CN=DL_%,..."]}
Is there any way to put that expression in the negative so i don't have to list all of the other groups?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
10/24/2022 09:55 AM
No You need to write all possible combination. You can't mention not in endpoints filter
Regards,
Rushikesh Vartak
If you find the response useful, kindly consider selecting Accept As Solution and clicking on the kudos button.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify a Moderator
11/07/2022 05:51 PM
@Avdupa1070 I understand the problem statement, and currently, it is not supported in our connector.
The entitlements imported as part of account import only have their entitlement_value populated and not the meta-data. We import those groups via account import as they are present in the memberOf attributes in the AD user objects.
- Generate Entitlement displayname from entitlement_value on import job in Identity Governance & Administration
- Active Directory Entitlement Import in Identity Governance & Administration
- Entitlement owner been removed after running access import in Identity Governance & Administration
- EPIC Accounts/Entitlement Import Queries in Identity Governance & Administration
- Symbol Character is Removed when Import Azure AD Entitlement in Identity Governance & Administration