- Saviynt Forums
- Saviynt Exchange
- Community Sourced Integrations
- Jama Software Integration Guide
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Notify a Moderator
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Notify a Moderator
05/18/2023 10:45 PM - edited 05/19/2023 07:33 AM
Disclaimer
The integration was either created by Saviynt or by Saviynt community users . The integration is available “as is” and fall under standard connectors support for REST, SOAP, JDBC, LDAP, PowerShell, Jar and Saviynt Connector Framework.
Understanding the Integration between EIC and Jama Software
Preface
This guide describes the integration between Saviynt Enterprise Identity Cloud (EIC) and Jama Software .
Audience
This guide is intended for administrators and target application integration teams responsible for implementing a secure integration service with Jama Software .
Introduction
Jama Software is the definitive system of record and action for product development. The company's modern requirements and test management solution helps enterprises accelerate development time, mitigate risk, slash complexity and verify regulatory compliance.Jama Connect brings people and data together in one place, providing visibility and actionable insights into the product development lifecycle.
The Jama Software connector enables you to seamlessly integrate with Jama Software to manage user lifecycle and govern access to their Usergroups.
For more information about different connectors in EIC, see Saviynt Enterprise Identity Cloud Connectors.
Note: This guide provides information about using the Jama Software REST connector using REST API for performing operations listed in the Supported Features.
Supported Features
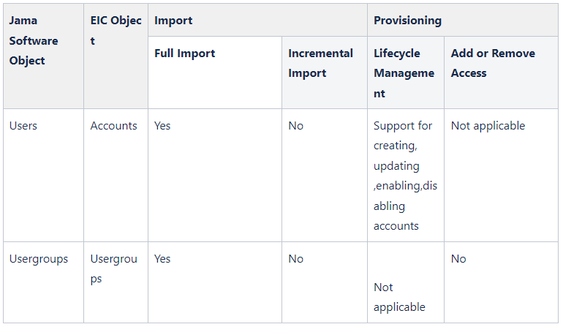
The Jama Software integration supports the following features:
Supported Software Versions
Software | Version |
EIC | Release v4.5 and later |
Understanding the Integration between EIC and Jama Software
You must create an integration between EIC and the collaboration platform hosted by the target application to perform import, provisioning, and deprovisioning tasks. The following components are involved in the integration:
The Complete Service Management platform Jama Software combines ITSM with ESM and SIAM capabilities, enabling all internal departments, such as IT, HR, and Facilities, as well as external service providers and customers, to collaborate securely and seamlessly on one complete platform, reducing complexity and improving productivity.
Objects are imported as entitlement types into EIC.
Security System represents the connection between EIC and the target application.
It comprises of an endpoint, which is the target application for which you want EIC to manage the identity repository.
It provides application instance abstraction from connectivity including high-level metadata. For more information about creating a security system, see Creating a Security System.
Endpoint is an instance of an application within the context of a security system.
It is the target application or application from which the connector imports the data and performs provisioning or deprovisioning of identity objects, such as users, accounts, and entitlements.
It is mandatory to create an endpoint after creating the security system.
You can associate a single security system with multiple endpoints if the deployment involves modelling of multiple isolated virtual applications (based on sets of specific entitlements according to certain categories) within a single application instance. For more information about creating an endpoint, see Creating an Endpoint for the Security System.
Connector is a software component that enables communication between EIC and the target application. It provides a simplified integration mechanism where in some instances you only need to create a connection with minimal connectivity information for your target application. The REST connector is used for importing, provisioning accounts and access through the REST APIs. For more information about creating a connection, see Creating a Connection.
Job Scheduler is a software component that executes a job based on the configured schedule to perform import or provisioning operations from EIC.
When a provisioning job is triggered, it creates provisioning tasks in EIC. When these tasks are completed, the provisioning action is performed on the target application through the configured connector. If you want to instantly provision requests for completing the tasks without running the provisioning job, you must enable Instant Provisioning at the security system level and the Instant Provisioning Tasks global configuration. For more information about the jobs used by the connectors in the Jama Software integration.
Integration Architecture
EIC uses a REST connection for integrating with Jama Software for importing data and for performing provisioning and deprovisioning tasks.
The following diagram illustrates the integration architecture and communication with the target application

Setting Up the Integration
Prerequisites
Perform the following steps to Generate & Setup token authentication
Request: POST
Target: /rest/oauth/token on your instance of the Jama application, e.g.: http://localhost:8080/jama/rest/oauth/token
Please Note, there is no training slash '/' after token
Data: grant_type=client_credentials
Authentication: HTTP Basic Authentication with client ID as user name, client secret as password
If your connection library does not support HTTP Basic Authentication, you may consider adding an additional header:
Name: "Authorization", value: "Basic AUTHORIZATION", where AUTHORIZATION is a Base64-encoded presentation of "ID:SECRET", where ID is the client ID and SECRET is the client secret
This will return a response that includes an access_token field, which is the access token used for the next leg. It also includes an expires_in field, which is the number of seconds until the access token expires (1 hour is the default). The access token can be used many times, until it expires.
Creating a Connection
Connection refers to the configuration setup for connecting EIC to target applications. For more information about the procedure to create a connection, see Creating a Connection.
Understanding the Configuration Parameters
While creating a connection, you must specify connection parameters that the connector uses to connect with the target application, define the type of operations to perform, the target application objects against which those operations are performed, and the frequency of performing them. In addition, you can view and edit attribute mappings between EIC and the target application, predefined correlation rules, and provisioning jobs and import jobs.
Configuration Parameters for Account and Access Import
The connector uses the following parameters for creating a connection and for importing account and access from the target application:
Connection Parameters
Parameter | Description | Example Configuration | Mandatory? |
|
|
Connection Name | Specify the name to identify the connection. | - | Yes |
|
|
Connection Description | Specify the description for the connection. | - | No |
|
|
Connection Type |
| - | Yes |
|
|
Default SAV Role | Specify this parameter to assign the SAV role for the connection. The SAV role is a role in EIC that assigns specific access to users. This parameter is valid only for importing users. Sample value: User assigned with the ROLE_ADMIN role, has access to all the sections of EIC. | - | No |
|
|
Email Template | Specify this parameter to select an email template for sending notifications. Email templates provide immediate trigger of emails to a user based on actions performed. Email informs user about the action performed and if critical, needs immediate action from the user. | - | No |
|
|
ConnectionJSON | Specify this parameter to create a connection.
Note: Update CLIENTID and CLIENTSECRET as per your Jama Software details. |
Refer to the Connection Package |
|
| Yes |
Import Parameters
Parameter | Description
| Recommended Configuration | Mandatory? |
AccountEntImport JSON | Specify this parameter to reconcile the accounts and entitlements |
Refer to the Connection Package |
Yes |
Configuration Parameter for Provisioning
Parameter | Description
| Recommended Configuration | Support for Binding Variables? | Support for Java Ternary Operations? |
CreateAccountJSON | Specify this parameter to create an account in the target application.
|
Refer to the Connection Package | The bindings supported are:
| Yes |
Update Account JSON | Specify this parameter to update an account in the target application. |
| The bindings supported are:
| Yes |
EnableAccountJSON | Specify this parameter to Enable an account in the target application. |
| The bindings supported are:
| Yes |
DisableAccountJSON | Specify this parameter to Disable an account in the target application. |
| The bindings supported are:
| Yes |
Importing Connection Package
connection package helps you build the connection with pre-defined JSONs, this can be used if your tenant does not already have out of the box connection templates available. Here are the steps to import the Jama Software connection package.
Download the connection package.
Navigate to Admin → Transport → select Import Package.
Browse the downloaded package and Import.
Navigate to Admin → Connections → Select “Jama Software ” Connection.
Edit the connection with your Jama Software tenant details.
Creating a Security System
The security system represents the connection between EIC and the target application. For more information on creating a security system, see Creating a Security System.
Creating an Endpoint for the Security System
Endpoint refers to the target application used to provision accounts and entitlements (access). For more information on creating an endpoint, see Creating Endpoints.
Using the Jama Software Integration
You can use the Jama Software integration for performing import and provisioning operations after configuring it to meet your requirements.
Guidelines for Using the Integration
You must apply the following guidelines for configuring import:
Run account import before running the access import.
Map all Jama Software attributes to EIC account attributes using ImportAccountEntJSON.
You must apply the following guidelines for configuring provisioning:
Use Java ternary operators if you want to add conditions in the provisioning parameters. You can use Java operations to tweak any attributes by using if-else conditions, substrings, or operators in the JSON for provisioning.
Configuring Import Operations
Full account import: When configuring the connection for the first time, first perform full import to import all existing accounts from the target application to EIC. To perform full import, the invoke API gets response from the target application and maps the attributes in the target application with attributes in EIC. As part of this process, the deleted accounts are also identified and marked as suspended from import service.
Full Access import: When configuring the connection for the first time, first perform full import to import all existing access from the target application to EIC. To perform full import, the invoke API gets response from the target application and maps the attributes in the target application with attributes in EIC. As part of this process, the deleted entitlements are also identified and marked as inactive.
The import jobs are automatically created in EIC after you create a connection for the Jama Software integration. For more information about creating jobs, see Data Jobs.
Importing Accounts and Accesses
You must import accounts after the users are available in EIC.
To import accounts:
Specify the connection and import parameters. For more information, see Account and Access import.
Note: Ensure that the connection type is selected as REST.Configure the Application Data Import (Single Threaded) job to import accounts and access. For more information, see Data Jobs.
Configuring Provisioning and Deprovisioning
Provisioning is automatically enabled when a connection is configured. For detailed information about performing provisioning tasks, see Access Request System.
To provision objects to the target application:
Specify the connection and provisioning parameters. For more information, see Configuration Parameters for Provisioning.
Note: Ensure that the connection type is selected as REST.Configure the Provisioning job (WSRETRY). For more information, see Provisioning Jobs.
When a provisioning job is triggered, it creates provisioning tasks in EIC. When these tasks are completed, the provisioning action is performed on the target application through the connector.
Troubleshooting
To troubleshoot common problems with connectors, answer frequently asked questions, and provide solutions to a few common issues you might encounter while configuring or working with connectors, see Common Troubleshooting Guide for Connectors.
To troubleshoot common problems or obtain answers for frequently asked questions for REST connectors, see the REST Connector Guide.
Note: Ensure that you record the token expiry duration during the initial token generation. The connection may fail, if the token is not refreshed.
